Nuclear terrorists apparently prefer Archos tablets
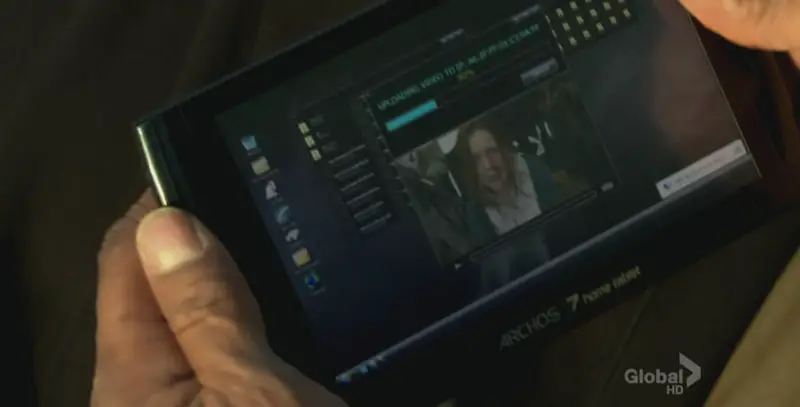
The latest TV episode of “NCIS: Los Angeles” that aired last night in the US had a story line that involved (spoiler alert) a stolen nuclear warhead. The bad guys’ plan was to release a video of it and posing as religious terrorists in order to get the stock market to crash and make a pretty penny with insider information. When the NCIS agents recover the nuke, one of them pulls an Archos 7 Home Tablet out from one of the terrorists’ pockets.
Judging from the screenshot, it’s apparently running either VNC or some other sort of remote control software in order to control a remote upload of the video file in question. In order to stop the upload (I guess it was only a remote viewer without any input control…?) their stay-at-base geeks “used a VNC controller to piggy-back the upload with a Trojan and corrupt the streaming data packets by initiating a stack buffer overflow”.
I don’t have much knowledge of that kind of computing and the statement had enough sensible words in it (compared to others) to make me have to ask our resident tech guru Yuki if it made any sense, which he assured me it didn’t- which is pretty typical of a TV show tech explanation. The fact they’re using a MAC address as an IP was also a clue, and so was the fact that the Archos 7 HT is Wifi-only (no 3G) and this was in the middle of a parking lot… The NCIS geek proceeded to state that his method “broke the Internet”, which caused another agent to worry about Twitter being down. In my experience, Twitter manages to crash perfectly frequently on its own without any help from NCIS.
I haven’t studied the Archos 7 Home Tablet specs in detail, but I’m fairly sure that breaking the Internet is not part of the list of features (knowing Archos devices, it’s more likely the Internet will break the tablet). At least it’s good to see that some people bought the Archos 7 Home tablet, despite it being a resistive touch screen device. Then again, maybe that’s the reason they had to crash the Internet to make it stop uploading, as I sure as hell wouldn’t want to try controlling a desktop OS by using my finger on that screen. Let’s just hope that if (Thor forbid) this scenario plays out in the real world, the terrorists choose a more competent tablet so that the special agents who have to stop them can disarm the threat themselves without breaking the entire Internet.

