Rooted Sense users face hurdles with phone encryption
 For the longest time I wondered why I would ever want to encrypt my phone. I wasn’t carrying around state secrets, I don’t work for a company with a lot of trade secrets, I’m not cheating on my wife – what would it matter if someone found my phone without phone encryption on?
For the longest time I wondered why I would ever want to encrypt my phone. I wasn’t carrying around state secrets, I don’t work for a company with a lot of trade secrets, I’m not cheating on my wife – what would it matter if someone found my phone without phone encryption on?
As part of the destroying data on your phone piece, caused mostly because Avast decided to be voyeurs with purchased and supposedly wiped cell phones, I decided to “hack” myself with my device and see what I could “learn.”
The short of it is I realized my phone is far too connected to be considered safe if lost. So I looked at phone encryption for everyday operating and realized that if you’re rooted, it presents its own challenges. If you’re rooted and on HTC Sense running with phone encryption, you’ve probably run into them, and this is probably stuff you already know.
I’ll preface the following with, if you have the bootloader unlocked or S-OFF, your chances of running a completely secure phone are probably a lot lower than stock. With an unlocked device, you’re able to push a boot environment that allows data to be copied to a computer for decryption; however, for the non tech savvy thief that’s probably not going to be an issue.
The first thing I found after encrypting my phone running a Sense ROM is that recovery just doesn’t work like it used to and is pretty much useless. That’s the first huge problem you’re going to face, as the data partition can’t be mounted, and anything useful seems to be inaccessible to recovery mode. You also supposedly can’t factory reset from there due to it not being able to mount the encrypted data stores, although I didn’t try this.
(Side note – AOSP and TouchWiz encryption are decryptable via TWRP according to the instructions, I’m betting ClockworkMod also, but I’m not running it at the moment. My issue involves an HTC One M8 running Sense, so chances are it’s just another Sense thing or my version of TWRP just doesn’t cut it.)
Factory resets have to be done from the bootloader menu as they’re the only level of operation that can touch those device encrypted HTC data stores.
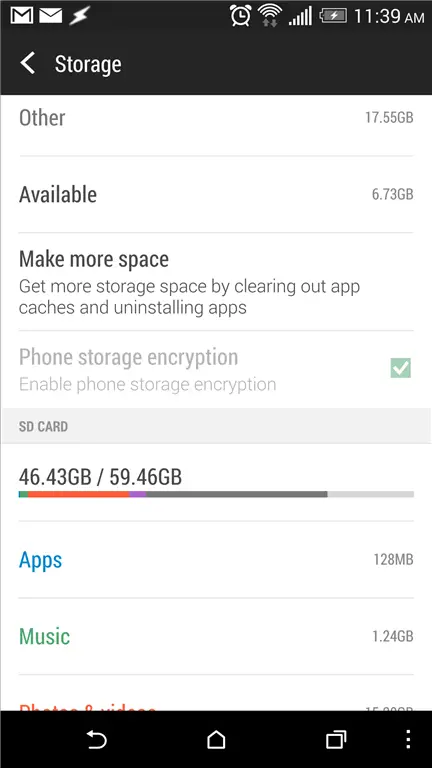
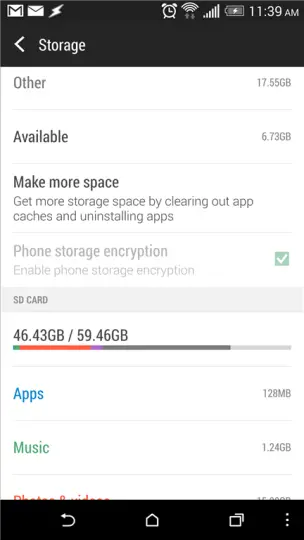
Once you’re encrypted, you’re faced with an interesting issue. Anything you’ve created that’s stored internally while encrypted is encrypted as well. This means photos stored to the internal SD card, Titanium Backup data stored internally, etc. You suddenly have a whole new set of data that will be destroyed or lost if you factory reset.
On an unencrypted phone, if I wanted to flash a mod safely I would drop to recovery, make a nandroid backup, flash the mod, and if it didn’t work I could jump back to the previously saved nandroid. On an encrypted Sense phone I can’t even mount the data store, although the /system partition is mountable. So if you’re willing to go nandroidless, or only back up the system, you should be good.
If your phone doesn’t boot after that however, you’re pretty much at the point of wiping and starting fresh.
Creating a full nandroid backup with phone encryption requires you use an Android-mode nandroid app such as Online Nandroid Backup and saving the nandroid data externally. If you save the nandroid data internally, well you’ve saved now-encrypted data and there’s no way to decrypt it.
Additionally there’s evidently no way to use anything but pattern or PIN unlock in Sense 6 when encrypted, and there’s no way to decrypt the device if you’re tired of dealing with encryption.
I’ve decided that rather than remain running encrypted, I’m going to probably jump back to the unencrypted side and move some of the TMI offline. It’ll make it a bit more annoying when I need it, but I can use whatever lock method I want and not have to deal with recoveries that don’t support HTC’s encryption methods and the possibility of losing all my data.