Dealing with 2-Step Verification problem apps
 So this morning I set up 2-Step Verification, and suddenly the mountain of Tasker projects using Google-enhancing plugins I’ve somewhat cobbled together stopped working, as well as some ancient applications I run on old devices.
So this morning I set up 2-Step Verification, and suddenly the mountain of Tasker projects using Google-enhancing plugins I’ve somewhat cobbled together stopped working, as well as some ancient applications I run on old devices.
This, combined with finding out I’ve been pounding my head against a drive mapping wall for the past week, might have ruined my day if Google didn’t already have a solution for apps that don’t work with its 2-Step Verification.
Many plugins, miscellaneous apps, and shell scripts have long been guilty of storing your passwords where they could be retrieved if someone had access to your phone, and 2-Step Verification pretty much puts an end to plain password authentication, so you might be wondering where’s you’re left when a relied-upon plugin just doesn’t work any more.
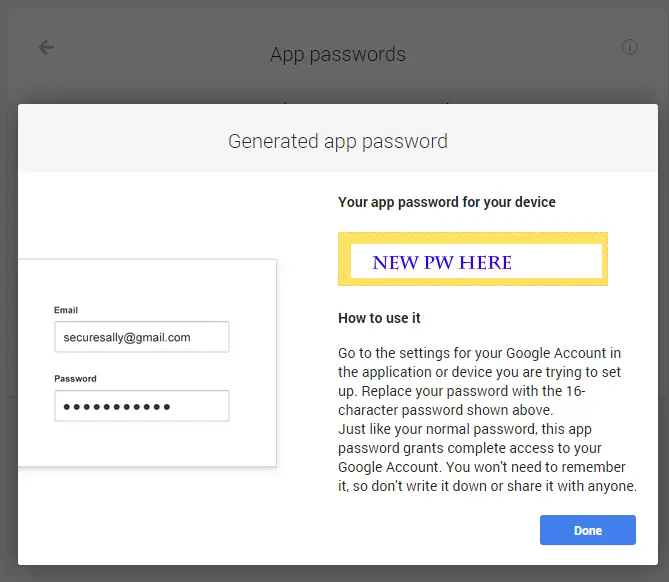
Luckily Google has an app-specific password page that will allow you to grant one app permission to access Google services with a stored 16-character password (19 if you count spaces).
Simply go over to your 2-Step Verification security page, click app passwords, add a new password, give the thing a name, now you can log into your account via plugin or antiquated app by using that specific password and your email address. Should you device become lost or you find out that nefarious hackers have been using your plugin login to send out spam email, you can simply revoke that app password and move on with your business.
I’m not sure at the moment how you can tell that someone is logging in with an app-specific password as the only things I see on my log are IP addresses, but I imagine if you had to bring Google security into the mix they could tell you which app password was being used and track down the culprit plugin, app, or shell script.