UU AppPurifier: root-style control for unrooted
 UU AppPurifier is an interesting application in that it gives an unrooted user some measure of root-style control over other applications, and the way it does it is really interesting. We’ll get into that but here are the feature highlights:
UU AppPurifier is an interesting application in that it gives an unrooted user some measure of root-style control over other applications, and the way it does it is really interesting. We’ll get into that but here are the feature highlights:
- Disable apps from auto launching
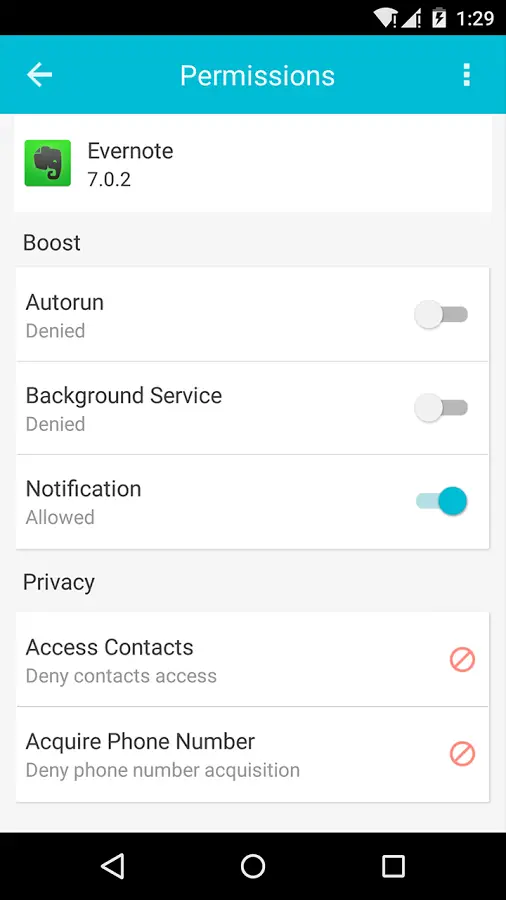
- Individual permission toggles for privacy
- Hide location and phone model by app
- Privacy invasion detection
You might not want an app launching at startup as that takes time from the boot. While small apps aren’t a huge deal, larger apps, or those with a lot of data can significantly slow your roll at boot time. Startup managers generally only work on rooted phones.
Permissions on unrooted phones have so far been “accept these, or don’t download”. UU AppPurifier can deny a permission such as precise GPS location and Camera Access to your child’s apps that don’t need it, thus not sharing pictures of your child and when they’re at home and when they’re away with some third party.
Some apps refuse to work on some phones, and UU AppPurifier can hide your phone model allowing you to use some things (although you’ll probably still have to install from something like APKMirror in order to get around the Play Store checking).
How it works
UU AppPurifier works by uninstalling the app you’re wanting to “purify,” then re-signing the app and changing the app’s manifest for whatever startup and permissions you require.
The new purified app has a different signature, permissions, startup options, and in essence is an entirely different program as far as the world is concerned. That being said, there will be no automatic purified updates for the app.
If an app doesn’t work after it’s processed, just uninstall and install the original.
Some drawbacks
As mentioned above the app now has a different signature, this means you’re not going to be able to auto-update, although perhaps the author of UU AppPurifier will get around to a market check and un-purify/install update/re-purify later.
Due to Android sandboxing, the uninstall and reinstall, your data for the app is probably going to get lost when you process it.
Is it safe?
The only thing you have to worry about here is the potential for the app developer to inject some code into the apps you’re dealing with. As you’re telling the app to take another app, strip it, change parts of it, and repackage it, if the developer wanted to stick something else in, chances are it wouldn’t be particularly hard to do.
My bet is an app developer can take a look at a purified app and the original and tell if anything other than the manifest has been modified pretty easily.
I don’t know, but the idea and the execution is nifty.
Download: Google Play