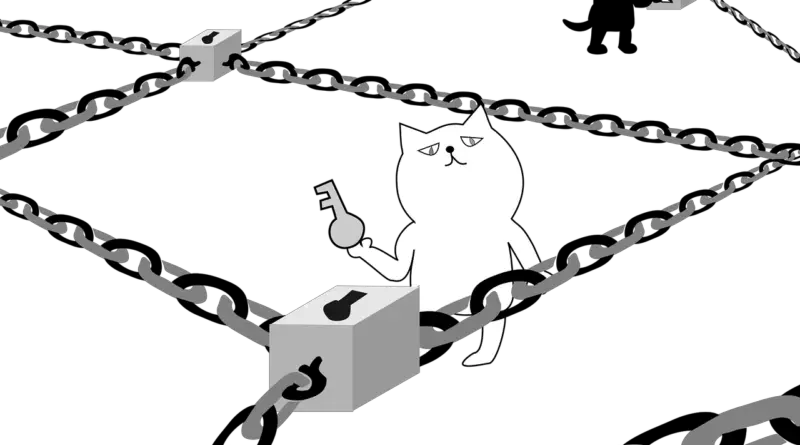
How hackers are bypassing two-factor authentication
My guess is this will be the big news story in the next few days of how two factor authentication is broken. It’s not, but you know the news.
The rundown is that hackers are now creating phishing websites that ask for your credentials (the usual,) and when the two factor authentication is required they simply trigger a request to Google or whatever service is to fire it off, and then your victim enters it in, thinking they’re on the correct site.
Two factor authentication works the same as it ever has, it’s not been cracked, it’s just slightly more sophisticated phishing is in effect. You’re still handing over all your information because you didn’t check that you were actually on the right website.

So yeah… you ever get prompted to enter a 2FA code when you don’t think you should, just step back and go to the web site or service in a browser with you typing the URL, not clicking it.
Hopefully the services that have 2FA in place will start checking originating IPs against your devices and send that along with the code “looks like the person requesting access is located in Cyprus, you sure you want to give them this code? 274122”
[Motherboard]