FrankSpeech sort of launches… maybe?
Mike Lindell (the My Pillow guy,) decided to launch Frank Speech and there’s been so many claims by him of biblical level hacking that was impeding the site from launch I decided to check out what exactly was being attacked. Long story about working for a dotcom and researching major failures 15 years ago omitted here.
Once you get to the site, you’ll get a live video of Lindell usually talking about being hacked or rehashing his OANN show where he claims the US election was stolen. He’s evidently doing a 48 hour live launch stream at the moment. This is the only part of the site I can find that works.
None of the linked articles are integrated with their social network so the question becomes why they’re there. There are no comments, message boards, any integration you might expect with a social network. No examples of what this platform is supposed to have.

I attempted to sign up for an account and was bombed out multiple times, and then started experimenting just to see what was going on. The Frank Speech new user registration page has your standard requirement, phone number, email address, username, password and confirm password, and a math question.
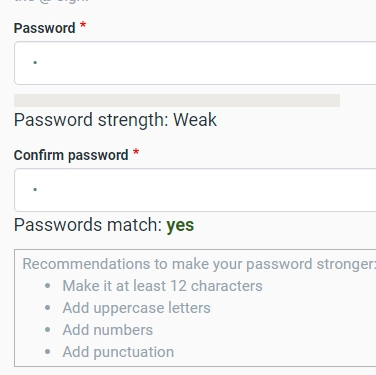
The math question, password, and the handle appear to be the only thing preventing you from posting the data through to the next page. If the password doesn’t match you’ll get a toast that it doesn’t, but there appear to be no requirements on the password and you can make it one character if you want.
If the phone number isn’t there, or you answer the 3 + 3 = cucumber (or CU as there’s a two character limit,) you post on to the next page.
The phone number validation script pops up helpful formatting options on any number real or fake that goes in it, and allows character input.

Passwords can be one character, are only validated if they match or not.
If you say you have an account and attempt to log in you’re met with the math challenge that isn’t validated anywhere in javascript or posted to the next page as far as I can tell from the code.
Every page says it was proudly built by Johnston Howse, which links to a landing page Rhubarb-Terrier-x8ya.squarespace.com – even the domain name JohnstonHowse.com just redirects there.

I’m very much of the belief this isn’t being hacked. It’s just not built yet beyond a landing page. It’s currently sitting behind Cloudflare, one of the best DDOS mitigation services on the planet, running Drupal 8 on what appears to be a well known shared hosting provider, so if it’s up, it’s probably running as coded.
Weird launch.


I registered but never got the email they were supposed to send. I see nothing on the website where I can post something. I hope they get things up and running soon.