Your IoT devices have no protection. You know that right?
With the recent #casthack that went on a lot of talk has been about how Google’s home products do not have any protection. They don’t, but they’re not the only things that don’t.
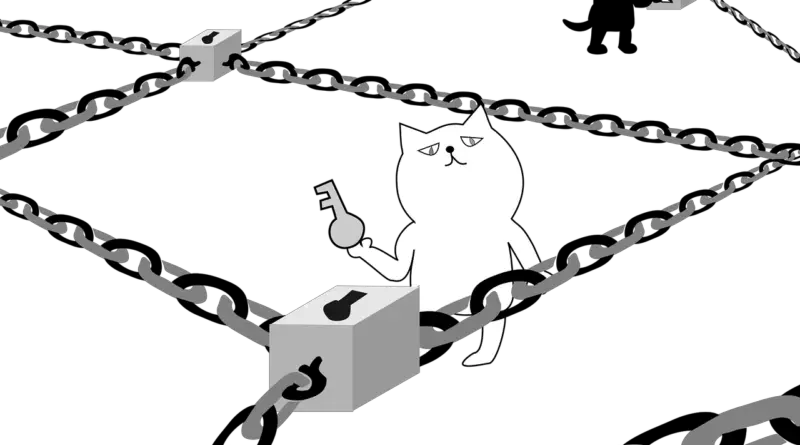
Pretty much any IoT thing you’ve got probably is not requiring authentication on a local network. All these little lightbulbs and smart plugs you can just remote into and issue a command and it accepts it. This is how IoT is designed. It’s not secure. They rely on your router and network for security.
All of these little smart devices – your TV, your Google Assistant, your internet connected foot tickler, none of these are passing off military grade authentication to each other, they’re just connecting over a local network they assume is secure.
Unfortunately, as many people learned with the casthack, if someone can get in your network your IoT is most likely theirs. All these things works so well together because there’s not a lot of hoops to jump through to turn on a lightbulb via the internet, there’s not a two factor authentication to turn off a plug.
Now, this shouldn’t be the case, but all this IoT garbage we’ve got makes the horrific assumption that either you or your ISP know something about basic security.
For those who need a refresher basic security involves:
- Passwords that aren’t reused and can’t be guessed
- No open access points for neighbors to get into
- A router that doesn’t let the outside world into your network
- Updating firmware for all devices regularly
Oh yeah, did you know your lightbulb had firmware and that it’s running a little stripped down linux with a telnet client in it? Yup. Your lightbulb has to be updated now.
Most ISPs are going to push security updates to your router you’re renting/getting from them. If you’re not renting, you’re in charge of getting firmware updates and making sure you’re not exposed to the internet via an external source being able to map internally from a crap implementation of UPnP.
But even if you’ve secured the internet, many of these devices can be attacked if you’re within WiFi range (this part’s a bit unlikely so feel free to skip this paragraph.) There’s a little trick where you de-auth a device. You can see an example of on-network deauth there. You can also spoof the AP name, and a host of attacks that actually work. None mentioned here is probably going to work for ya.
There are plenty of companies out there trying to sell you a solution to this lack of security. Most work for now. Only decent security solution I’ve seen is complete WiFi isolation and locking the device to only talking to set IPs, but that prevents discovery.
So guard your gate if you can (router,) but be aware you’re putting a bunch of little exploitable devices that may never see another firmware update ever into your network.
Also be aware when you tell a light to turn on, generally you’re telling a server out in the internet to tell another set of servers to create a notification for the light to pick up and turn on. I read a while back that it takes somewhere on the order of 24 servers maintained by three companies to turn on a lightbulb and that’s the new joke.
If any one of those breaks you’re in the dark.
But yeah, be aware if someone breaks in your network for any reason chances are very good that all your internet connected stuff generally can be found and controlled, without passwords, by someone using strobe and telnet.